ISO 27001
How Long Does ISO 27001 Certification Take With and Without Automation?
ISO 27001 Certification Timeline: Manual vs. Automation
"How long does ISO 27001 certification take?" The classic consultant answer: it depends.
And it's true. Timeline depends on your company's size, how mature your security posture already is, and, most critically, whether you handle compliance manually or through automation.
For most organizations, certification takes between 3 and 12 months. The gap between those numbers isn't about effort. It's about method.
When enterprise customers ask for your ISO 27001 certificate, they're not looking for a checklist - they want evidence of a living, breathing ISMS behind it. That makes the question pressing: how do you get there fast, without burning out your engineering team or cutting corners that haunt you during audit?
Let's break it down.
What Is the Typical ISO 27001 Certification Timeline?
Every company navigates the same structural phases regardless of size or approach. Here's what to expect:
Gap Analysis (2 - 4 weeks): Assess your current security posture against ISO 27001 requirements. Identify missing policies, broken controls, and unmonitored assets.
Risk Assessment and Treatment (4 - 8 weeks): Identify threats, score risks, and define how you'll mitigate, avoid, transfer, or accept them. This is the core engine of your ISMS.
ISMS Implementation (2 - 6 months): The heaviest lift. Write policies, roll out controls, change organizational processes, and generate artifacts that prove those controls work.
Internal Audit (2 - 4 weeks): An independent review of your ISMS before external auditors arrive.
Certification Audit - Stage 1 and Stage 2 (4 - 8 weeks): Stage 1 is a documentation review. Stage 2 is a deep operational dive into your controls.
A 50-person SaaS company with a cloud-native stack will move faster than a 500-person organization running legacy on-premise infrastructure. But the phases don't change, only the speed through them.
ISO 27001 Without Automation: When Manual Works, and When It Doesn't
Manual compliance gets a bad reputation it doesn't always deserve. For early-stage or small companies, it can be the right call - lower cost, full control, and proximity to requirements that helps you genuinely understand your risks.
Manual is likely sufficient if:
You have in-house ISO 27001 expertise
Your team is under 20 people and decisions move fast
Your tech stack is cloud-native and easy to document
You're not yet fielding enterprise-level security reviews
You're not regularly adding new systems or products
The cost of a GRC platform outweighs the benefit at your current stage
If most of these apply, stick with manual for now. But watch for the warning signs because they don't announce themselves. They creep in.
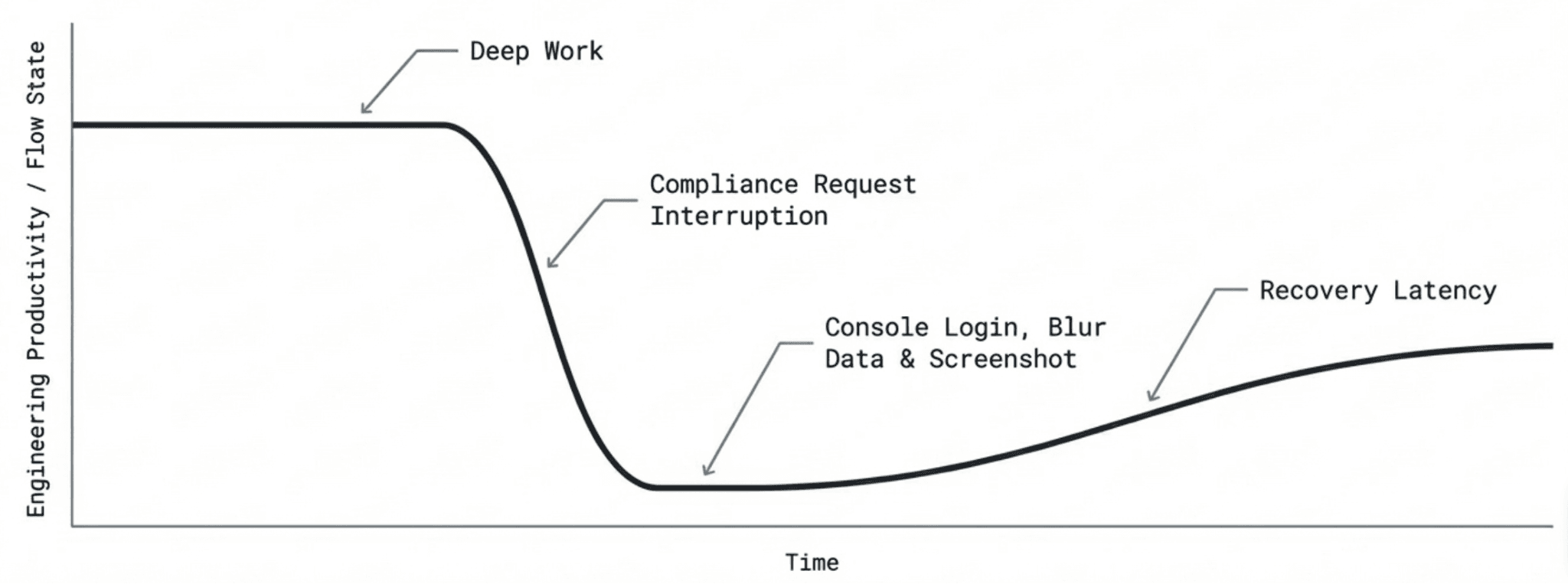
It starts small. An engineer gets pinged on Slack: "Hey, can you grab a screenshot of the access control settings in AWS?" They stop what they're doing, log into the console, navigate to the right panel, blur out the sensitive fields, screenshot it, and paste it back. Ten minutes, maybe fifteen. No big deal.
Except it happens again the next day. And the day after that. And each time, it's not just the minutes lost - it's the flow state broken. The mental context they have to rebuild after. The feature that gets delayed because the person who owns the architecture was busy hunting evidence for an audit that's still six weeks away.
That's the engineering tax. And it compounds quietly until it's everywhere.
Policy approvals start sitting in inboxes. A risk register gets updated in February and no one touches it until October, by which point three new systems have been onboarded, two vendors have changed, and the document describes a company that no longer exists. An auditor asks for proof that MFA was enforced on the date of a security review. Someone starts digging through Slack archives and email threads trying to reconstruct it.
This is what manual compliance looks like at scale. Not chaos - just constant, low-grade friction that quietly drains your most expensive people.
The real bottlenecks in a manual environment:
Policy creation and approvals: Writing an Information Security Policy from scratch takes weeks. Routing a Word document through legal, HR, and engineering adds more.
Evidence collection: Humans don't reliably remember to screenshot access reviews or export configuration logs. Human memory is not a compliance strategy.
Static risk assessments: A spreadsheet-based risk register is outdated the moment you close it. It has no real-time connection to your actual infrastructure.
In a manual environment, expect your ISO 27001 timeline to land in the 6-12 month range, sometimes longer. The bigger cost isn't time, it's the engineering hours bled into compliance admin, one interrupted flow state at a time.
ISO 27001 With Automation: How GRC Platforms Cut the Timeline
When you automate, the ISO 27001 implementation timeline typically drops to 1-3 months, depending on your baseline readiness.
A modern GRC platform shifts the burden of proof from people to software. Here's what gets automated:
Policy templates: Start with auditor-approved, framework-mapped templates. Customize and sign digitally - no blank-page problem.
Control mapping: Map one technical control across multiple frameworks. Test once, comply with many.
Evidence collection: Native API integrations with AWS, GitHub, Google Workspace, and Jira pull telemetry automatically. No more manual screenshots.
Risk tracking: Asset inventories and risk registers become dynamic. New vulnerability detected? New employee onboarded? The platform updates automatically.
The result: audit readiness shifts from a last-minute fire drill to a managed background process. Your engineers reclaim the hours they were losing to compliance admin.
Key Factors That Impact Your Timeline
Even with automation, these variables determine exactly how fast you reach certification:
Organization size and complexity: More people, more departments, more access reviews
Existing security maturity: SOC 2 compliant already? You have a significant head start
Internal vs. external expertise: A dedicated compliance manager or vCISO makes a material difference
Tech stack complexity: A clean cloud-native stack audits faster than sprawling infrastructure with shadow IT
Baseline documentation readiness: How much is already mapped and monitored?
Automation vs. manual: Still the single biggest lever you can pull
How to Get Certified Faster Without Cutting Corners
Speed without structure backfires. A fast-track approach that skips ISMS fundamentals will surface problems during your first audit - not before it. Focus on these:
Start with a gap assessment. You can't fix what you haven't mapped. Isolate which controls need engineering work and which just need documentation.
Use pre-built frameworks and templates. The control requirements for ISO 27001 are standardized. Your documentation approach should be too.
Assign clear ownership. A control without an owner is a control that will fail. Every policy, system, and risk needs a designated accountable human.
Implement continuous monitoring. If a developer disables a firewall rule and forgets to re-enable it, you need an alert, not an auditor finding it six months later.
Deploy a GRC platform when complexity demands it.
Tools like Vamu provide pre-approved templates, integrate with your stack to pull evidence automatically, notify you when something changes, and keep your ISMS audit-ready year-round.
The Bottom Line
Manual compliance isn't wrong - it's finite. For small teams with simple environments, it keeps costs down and puts you close to the requirements. That's a real advantage, at least early on.
But complexity doesn't announce itself. It accumulates. One more system. One more vendor. One more enterprise prospect asking for your SOC 2 and ISO 27001 in the same email. And suddenly your compliance program is running on the goodwill of engineers who have better things to do than hunt screenshots and chase approvals.
The engineering tax is real. Every interrupted flow state, every stale risk register, every policy sitting unsigned in someone's inbox - it all has a cost. It shows up in delayed releases, stretched timelines, and a security posture that looks fine on paper but hasn't been touched in months.
Automation doesn't eliminate the work. It eliminates the friction. Evidence gets pulled automatically. Risk registers stay live. Your team stays focused on building while your ISMS stays audit-ready in the background.
If the cracks are already showing, don't wait for a failed audit to force the decision.
Ready to get out from under the engineering tax? Book a demo with Vamu and see what continuous, automated compliance actually looks like in practice and how it helps you compliance and certification readiness for ISO 27001.